Outlook is a very capable email client and is widely available in business settings. Perhaps because of its availability, and users’ familiarity with it, many eDiscovery and digital forensics practitioners and litigation support professionals use Outlook to collect mailboxes for legal use.
On the surface, this looks reasonable—Outlook connects to email servers, downloads messages and saves them in PST format which is easily ingestible by eDiscovery and computer forensics tools. That said, Outlook is not your best choice to make a forensic copy of a mailbox. Here are 7 reasons why:
1. Outlook Does Not Connect to Email Servers in a Read-Only Manner
Let’s say that you are tasked with downloading emails from an IMAP server such as Yahoo. The IMAP protocol contains commands that can be used by forensic tools to operate on the mailbox in a read-only manner. For example, the EXAMINE command selects a mail folder in a read-only manner and does not allow changes, including changes to the \Recent flags of messages. Since Outlook is not designed for forensic use, it uses standard read/write commands such as SELECT.
Additionally, there is nothing preventing Outlook from causing changes to be made to the mailbox via its user interface. Yes, you can configure Outlook so that it does not mark previewed messages as “Read”, and it does not automatically classify any downloaded messages as “Spam” and move them to the “Junk Mail” folder. But how about if you accidentally dragged a message from one folder to another, or if you accidentally deleted a message? Using a general-purpose email client that syncs a mailbox both ways for forensic preservation is taking an unnecessary risk.
2. Outlook Is Slow
Outlook is not designed for bulk downloading of mailboxes. Once you configure a new IMAP email account, it starts by downloading message headers and presenting a reasonably usable user interface as soon as possible to get you started. On the other hand, most webmail providers have strict limits on bandwidth and number of requests, and they start throttling downloads. A forensic email preservation tool designed to download entire mailboxes as efficiently as possible can run circles around Outlook in terms of download speed and reliability.
3. Downloading Gmail Mailboxes Using Outlook Causes Duplication
Gmail has a different take on mail folders. Instead of using folders, users can apply overlapping labels to messages. This opens the door to lots of organizational possibilities.
When Gmail is accessed over IMAP, the labels are presented as virtual folders and if a message has a certain label applied to it, it would be listed under that virtual folder. The downside of this approach is that when a message has several labels applied to it, you download it several times under each virtual folder that corresponds to a label. So, depending on how labels were applied, you might be downloading the mailbox several times over.
On the other hand, using a forensic tool that accesses Gmail via Gmail’s API, you can download each message once and get a listing of all of the labels that were applied to it.
4. Outlook Does Not Allow IMAP or Gmail Server-Side Searches
Yes, Outlook has built-in search functionality. However, searches work after an IMAP or Gmail mailbox has been downloaded. On the other hand, using forensic email collection tools, you can execute searches on IMAP and Gmail mailboxes directly on the server before downloading any messages. These searches would not be as powerful as searches you could perform with eDiscovery and digital forensics tools after the collection (especially in terms of the ingestion and searching of attachments), but they can be a lifesaver for narrowing the scope down by simple criteria such as the dates, senders, recipients or subjects of top-level email messages.
5. You Might Be Missing Messages
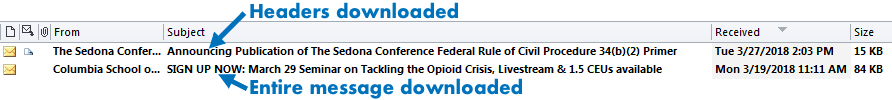
When connecting to an IMAP mailbox, Outlook first downloads message headers only to save time. These items appear very similar to fully downloaded messages, but they are still missing their message bodies and attachments (see below).
Figure 1 — Partially downloaded message vs. fully downloaded message in Outlook
You can define a Send/Receive Group in Outlook to configure it to download full message bodies. However, even then, it is not uncommon to run into straggler messages that are still missing their message bodies and attachments.
You would have to perform quality control repeatedly and meticulously to make sure all messages have been completely downloaded. Forensic email collection tools work differently—messages are either fully downloaded, or they are not.
6. You Will Need The Custodian’s Password with Outlook
Let’s imagine that you are planning to download a custodian’s emails from Gmail using Outlook. Before you start, you would ask the custodian for their password—or an App password if they are using two-factor authentication. The password gives you access to much more than their email—you could access other Google services that the custodian uses such as Google Drive, Photos, Hangouts, etc.
Additionally, in order to access Gmail via Outlook, you would have to allow less secure apps in the custodian’s Gmail mailbox or enable two-factor authentication and generate an App password.
On the other hand, using tools specifically designed for forensic email acquisition, you can simply ask the custodian to authenticate the forensic collection software into their account on their own computer. During the authentication process, they can verify that the software only has access to their emails. Once the acquisition is complete, they can remove access to the software without having to change their password.
7. You Will Be Missing Detailed Logs and Hashes
A well-designed forensic tool makes documentation a breeze. For instance, if you are collecting an IMAP mailbox, forensic email collection software would provide a detailed log of IMAP commands sent to the server and the server’s responses, along with any encountered errors and details of the acquisition. Additionally, cryptographic hashes (e.g., MD5, SHA-1) of downloaded items would be calculated automatically.
Needless to say, you do not get these using Outlook. You can make up for some of this information yourself by meticulously documenting all of your actions, and manually hashing downloaded data. That said, you will not have access to behind-the-scenes information such as IMAP logs.
Conclusion
You might find it appealing to use a general-purpose email client such as Outlook, Thunderbird or Zimbra Desktop to preserve the contents of a mailbox for legal use. Don’t. These tools are not designed for forensic use and they pose a significant risk of altering the target mailbox needlessly. Furthermore, you will be spending way more time rectifying partial downloads and documenting your actions than if you used a forensic tool that did the heavy lifting for you.